Comprehensive Proxy Server Guide: Types, Applications, and Developer Examples
Proxy servers offer improved performance, security, and privacy. Here, learn about proxy server types including forward, reverse, transparent, SOCKS, and more.
Join the DZone community and get the full member experience.
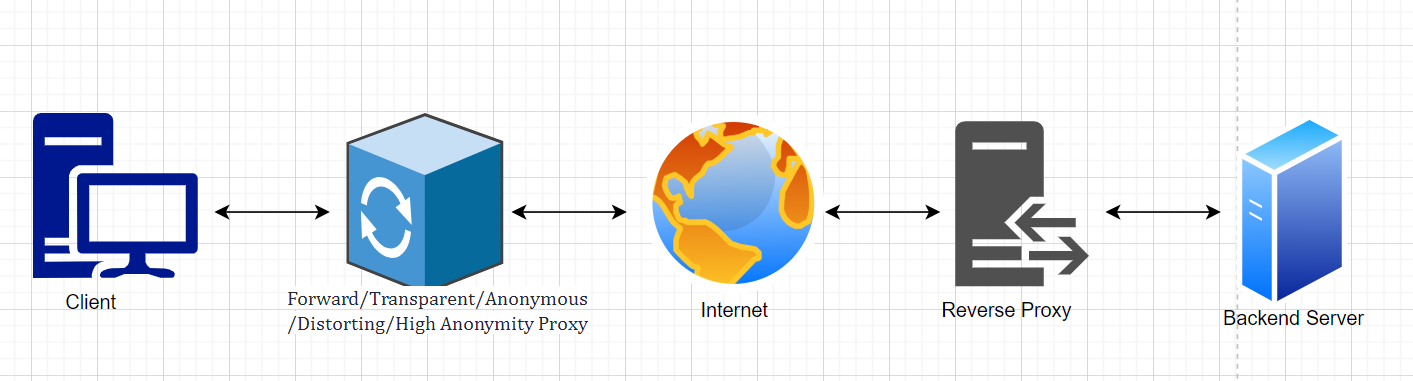
Join For FreeProxy servers are an essential component in the world of networking and web development. They act as intermediaries between clients and servers, providing several benefits such as improved performance, security, and privacy. In this article, we will discuss various types of proxy servers, their use cases, and provide code examples and an architecture diagram to help developers understand when and how to use them.
Types of Proxy Servers
Forward Proxy
A forward proxy is the most common type of proxy server. It sits between a client and the internet, forwarding client requests to the desired servers. Forward proxies can be used for caching, load balancing, and content filtering, among other things.
Use Case
A company might use a forward proxy to enforce internet usage policies or to cache frequently accessed content for faster delivery to its employees.
Code Example
Python with the requests library:
import requests
proxies = {
'http': 'http://proxy.example.com:8080',
'https': 'http://proxy.example.com:8080'
}
response = requests.get('http://example.com', proxies=proxies)
print(response.text)Reverse Proxy
A reverse proxy acts as an intermediary between the internet and one or more backend servers. It can distribute incoming requests to different servers, cache content, and provide additional security features.
Use Case
A website with high traffic might use a reverse proxy to distribute incoming requests across multiple servers to balance the load and optimize response times.
Code Example
Nginx configuration:
http {
upstream backend {
server backend1.example.com;
server backend2.example.com;
}
server {
location / {
proxy_pass http://backend;
}
}
}
Transparent Proxy
A transparent proxy is a type of forward proxy that intercepts client requests without requiring any configuration on the client side. It can be used for caching, content filtering, and monitoring network usage.
Use Case
An ISP might use a transparent proxy to cache popular content, reducing bandwidth usage and improving performance for its customers.
Code Example
Squid configuration:
http_port 3128 transparent
cache_mem 256 MB
maximum_object_size_in_memory 512 KB
cache_dir ufs /var/spool/squid 100 16 256SOCKS Proxy
A SOCKS proxy is a more versatile type of proxy that supports any network protocol and operates at the transport layer. It is commonly used for providing secure access to internal networks or bypassing network restrictions.
Use Case
A developer working remotely might use a SOCKS proxy to securely access their company's internal resources.
Code Example
Python with the requests library and socks module:
import requests
import socks
import socket
socks.set_default_proxy(socks.SOCKS5, 'proxy.example.com', 1080)
socket.socket = socks.socksocket
response = requests.get('http://example.com')
print(response.text)Anonymous Proxy
An anonymous proxy is a type of forward proxy that hides the client's IP address from the target server, making it difficult for the server to trace the request back to the original client. This helps users maintain their privacy and anonymity while browsing the web.
Use Case
A user concerned about online privacy might use an anonymous proxy to prevent websites from tracking their browsing activity.
Code Example
Python with the requests library:
import requests
anonymous_proxy = 'http://anonymousproxy.example.com:8080'
proxies = {
'http': anonymous_proxy,
'https': anonymous_proxy
}
response = requests.get('http://example.com', proxies=proxies)
print(response.text)Distorting Proxy
A distorting proxy is similar to an anonymous proxy, but it takes privacy a step further by modifying the client's IP address information in the request headers. This can make it even more difficult for the target server to trace the request back to the original client.
Use Case
A user seeking enhanced privacy and anonymity might use a distorting proxy to obfuscate their true IP address and location.
Code Example
Python with the requests library:
import requests
distorting_proxy = 'http://distortingproxy.example.com:8080'
proxies = {
'http': distorting_proxy,
'https': distorting_proxy
}
response = requests.get('http://example.com', proxies=proxies)
print(response.text)High Anonymity Proxy (Elite Proxy)
A high anonymity proxy, also known as an elite proxy, provides the highest level of privacy and security among proxy servers. It not only hides the client's IP address but also conceals the fact that a proxy is being used. This makes it extremely difficult for the target server to detect the presence of a proxy or trace the request back to the original client.
Use Case
Users who require maximum privacy and anonymity, such as whistleblowers or political dissidents, might use a high anonymity proxy to protect their identity and avoid potential repercussions.
Code Example
Python with the requests library:
import requests
elite_proxy = 'http://eliteproxy.example.com:8080'
proxies = {
'http': elite_proxy,
'https': elite_proxy
}
response = requests.get('http://example.com', proxies=proxies)
print(response.text)Architecture Diagram![Architecture diagram]()
Conclusion
Proxy servers provide numerous benefits in networking and web development, including improved performance, security, and privacy. By understanding the different types of proxies and their use cases, developers can make informed decisions about when and how to implement them in their projects. The code examples and architecture diagram provided in this article should serve as a starting point for developers looking to integrate proxy servers into their applications. However, it is essential to consider the risks and downsides associated with each type of proxy, especially when using open proxies or proxies designed for anonymity, to ensure the best balance of security, performance, and reliability.
Happy learning!!
Opinions expressed by DZone contributors are their own.

Comments