23 Docker Security Tools Compared
Discover and compare more than 20 Docker security tools, choose the best for your team, and learn how to implement them.
Join the DZone community and get the full member experience.
Join For FreeThere are quite a few Docker security tools in the ecosystem. How do they compare? This is a comprehensive list of Docker security tools that can help you implement some of the container security best practices.
Is Docker insecure? Not at all. Actually, features like process isolation with user namespaces, resource encapsulation with cgroups, immutable images and shipping the minimal software and dependencies reduce the attack vector providing a great deal of protection. But, is there anything else we can do?
There is much more than image vulnerability scanning and these are 23 container and Docker-specific security tools that can help.
1. Anchore Navigator

Homepage: https://anchore.io/
License: Commercial, some services are free to use.
Use Cases: Pre-production analysis, vulnerability newsfeed.
Anchore Navigator provides a free service for deep inspection of public Docker images. You can also explore their rich repository of already-dissected images for full visibility of its content, build process, and discovered CVE threats together with a link to the complete issue description and known fixes.
Using this tool you can perform a thorough analysis of your own images and subscribe to the images you frequently use for your deployments to receive timely security warnings.
2. AppArmor

Homepage: http://wiki.apparmor.net
License: Open Source.
Use Cases: Runtime protection, Mandatory Access Control (MAC).
AppArmor lets the administrator assign a security profile to each program in your system: filesystem access, network capabilities, link and execute rules, etc.
It's a Mandatory Access Control (or MAC) system, meaning that it will prevent the forbidden action from taking place, although it can also report profile violation attempts.
AppArmor it's sometimes considered a more accessible and simplified version of SELinux, both are closely related. You only need to learn the profile language syntax and fire your favorite editor to start writing your own AppArmor rules.
Docker context: Docker can automatically generate and load a default AppArmor profile for containers named docker-default. You can create specific security profiles for your containers or the applications inside them.
3. AquaSec

Homepage: https://www.aquasec.com/
License: Commercial.
Use Cases: Pre-production analysis, runtime protection, compliance and audit, etc.
4. Black Duck Docker Security

Homepage: https://www.blackducksoftware.com
License: Commercial.
Use Cases: Pre-production analysis, vulnerability newsfeed, license/legal assessment.
Black Duck Hub specializes in container inventory and reporting image inventory, mapping known security vulnerabilities to image indexes, and cross-project risk reports. You can easily pinpoint the specific libraries, software packages or binaries that are causing the security risk and the assistant will automatically offer you a list of known fixes.
As opposed to similar solutions, Black Duck Hub also analyzes the "License Risk" considering the different software licenses that you are currently bundling together to deploy your containerized distributed system.
5. Cilium

Homepage: https://www.cilium.io/
License: Open Source.
Use Cases: HTTP-layer security, network-layer security.
Cilium provides transparent network security between container applications. Based on a new Linux kernel technology called eBPF, it allows you to define and enforce both network-layer and HTTP-layer security policies based on container/pod identity.
Cilium leverages BPF to perform core data path filtering, mangling, monitoring, and redirection. These BPF capabilities are available in any Linux kernel version 4.8.0 or newer.
6. Cavirin

Homepage: https://cavirin.com
License: Commercial.
Use Cases: Runtime protection, pre-production analysis, compliance and audit
Cavirin works with organizations such as CIS to collaboratively develop and maintain the security standards that any other tool can benefit from. At present, it has authored CIS Docker Security Benchmark as well as CIS Kubernetes Security Benchmark. They have minted the term "DevSecOps" to stress their focus on integrating the security and DevOps/container fields. Apart from the features, you can expect in a one-stop DevOps security platform (maybe comparable to Twistlock or AquaSec in their feature proposal and approach), we can highlight their compliance and audit tooling for security standards like PCI, HIPAA, NIST or GDPR.
7. CoreOS Clair

Homepage: https://coreos.com/clair/docs/latest/
License: Open Source.
Use Cases: Pre-production analysis, vulnerability newsfeed.
Clair is an open-source project for the static analysis of vulnerabilities in containers (currently supporting AppC and Docker). Clair periodically refreshes its vulnerability database from a set of configured CVE sources, scrubs the available container images, and indexes the installed software packages. If any insecure software is detected, it can alert or block deployment to production.
Since Clair image analysis is static, containers never need to be actually executed, so you can detect a security threat before it's running in your systems. Clair is the security engine that CoreOS Quay registry uses internally.
8. Docker Capabilities and Resource Quotas

Homepage: https://www.docker.com
License: Open Source.
Use Cases: Runtime protection, resource DoS protection.
We shouldn't forget the basic security measures that come already bundled with our OS and the Docker engine.
Resource abuse and denial of service is an often overlooked but very real security problem in a containerized environment with vast amounts of software entities competing for the host resources.
Control Groups (cgroups) is a feature of the Linux kernel that allows you to limit the access processes and containers have to system resources such as CPU, RAM, IOPS, and network.
Capabilities allow you to break down the full root permissions into several split permissions, this way you can remove specific capabilities from the root account or augment the capabilities of user accounts at a more granular level.
9. Docker-Bench Security

Homepage: https://github.com/docker/docker-bench-security
License: Open Source.
Use Cases: Compliance and security audit.
The Docker Bench for Security is a meta-script that checks for dozens of common best practices around deploying Docker containers in production.
This script is conveniently packaged as a Docker container, just copying and pasting the docker run one-liner from its homepage you can instantly see the results of approximately 250 checks for your running Docker containers and the host running the Docker engine (Docker CE or Docker Swarm). Docker Bench tests are inspired by the CIS Docker Community Edition Benchmark v1.1.0.
10. Dockscan

Homepage: https://github.com/kost/dockscan
License: Open Source.
Use Cases: Compliance and audit.
Dockscan is a simple Ruby script that analyzes the Docker installation and running containers, both for local and remote hosts.
It's easy to install and run with just one command and can generate HTML report files. Dockscan reports configured resource limits, containers spawning too many processes or with a high number of modified files, also if your Docker host is allowing containers to directly forward traffic to the host gateway, to name a few examples.
11. Falco

Homepage: https://www.sysdig.org/falco/
License: Open Source.
Use Cases: Runtime alerting, forensics.
Sysdig Falco is an open-source, behavioral monitoring software designed to detect anomalous activity based on the Sysdig monitoring technology. Sysdig Falco also works as an intrusion detection system on any Linux host.
Falco is an auditing tool as opposed to enforcement tools like Seccomp or AppArmor. It runs in userspace, using a kernel module to retrieve system calls, while other similar tools perform system call filtering/monitoring at the kernel level. One of the benefits of a user-space implementation is being able to integrate with external systems like Docker, Docker Swarm, Kubernetes, Mesos, etc. and incorporate their metadata and tags.
Docker context: Falco supports container-specific context for its rules. Using this tool you can monitor the containers' behavior without instrumenting or modifying them in any way. Custom rule creation is very easy to grasp and the default rules file comes prepopulated with sane defaults.
12. HashiCorp Vault

Homepage: https://www.vaultproject.io/
License: Free with enterprise version.
Use Cases: Secure container-aware credentials storage, trust management.
Hashicorp's Vault is an advanced suite for managing secrets: Passwords, SSL/TLS certificates, API keys, access tokens, SSH credentials, etc. It supports time-based secret leases, fine-grained secret access, on-the-fly generation of new secrets, key rolling (renewing keys without losing access to secrets generated using the old one), and much more.
Vaults keeps a detailed audit log to keep track of all the secrets and the access and manipulations performed by each user/entity, so operators can easily trace any suspicious interaction.
Docker context: The secure distribution and traceability of secrets is a core concern in the new microservices and containerized environments, where software entities are constantly spawned and deleted. Vault itself can be deployed as a Docker container.
13. NeuVector

Homepage: http://neuvector.com/
License: Commercial.
Use Cases: Runtime protection, compliance and audit.
NeuVector focuses on real-time security protection at runtime, automatically discovers the behavior of applications, containers, and services, detects security escalations and other related threats in a similar fashion to other Linux IDS. NeuVector privileged ‘enforcer’ containers are deployed on each physical host, with full access to the local Docker daemon, apart from that, the internal technology used by NeuVector is not thoroughly detailed in the publicly accessible documentation.
NeuVector aims to be a non-intrusive, plug-and-play security suite, performing automatic discovery of running containers and their default behavior to assist and counsel the operators in the design of their infrastructure security profiles. NueVector focuses on container network security rather than the underlying system like many of the other run-time players.
14. Notary
Homepage: https://github.com/docker/notary
License: Open Source
Use Cases: Trusted image repository, trust management, and verifiability.
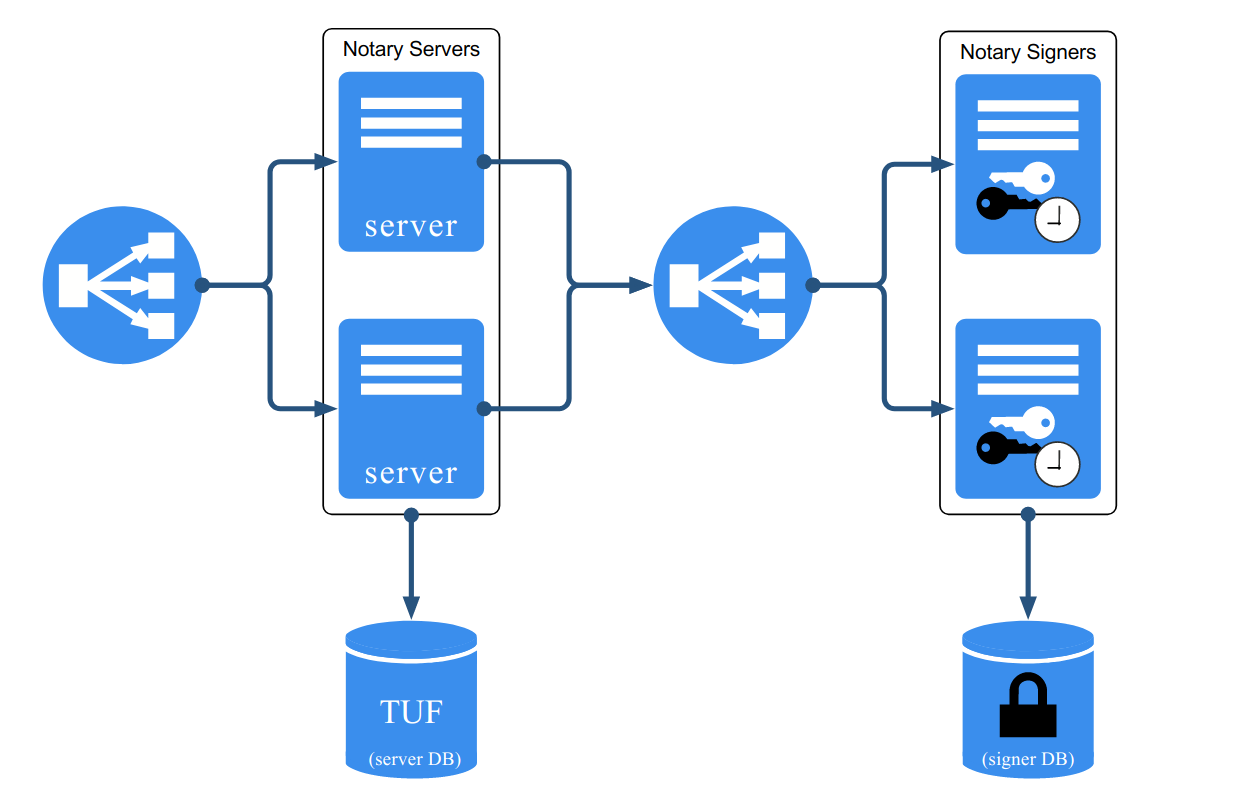
Image forgery and tampering is one major security concern for Docker-based deployments. Notary is a tool for publishing and managing trusted collections of content. You can approve trusted published and create signed collections, in a similar fashion to the software repository management tools present in modern Linux systems, but for Docker images.
Some of Notary goals include guaranteeing image freshness (most up-to-date content, to avoid known vulnerabilities), trust delegation between users or trusted distribution over untrusted mirrors or transport channels.
15. OpenSCAP
Homepage: https://www.open-scap.org/
License: Open Source.
Use Cases: Compliance and audit, certification.
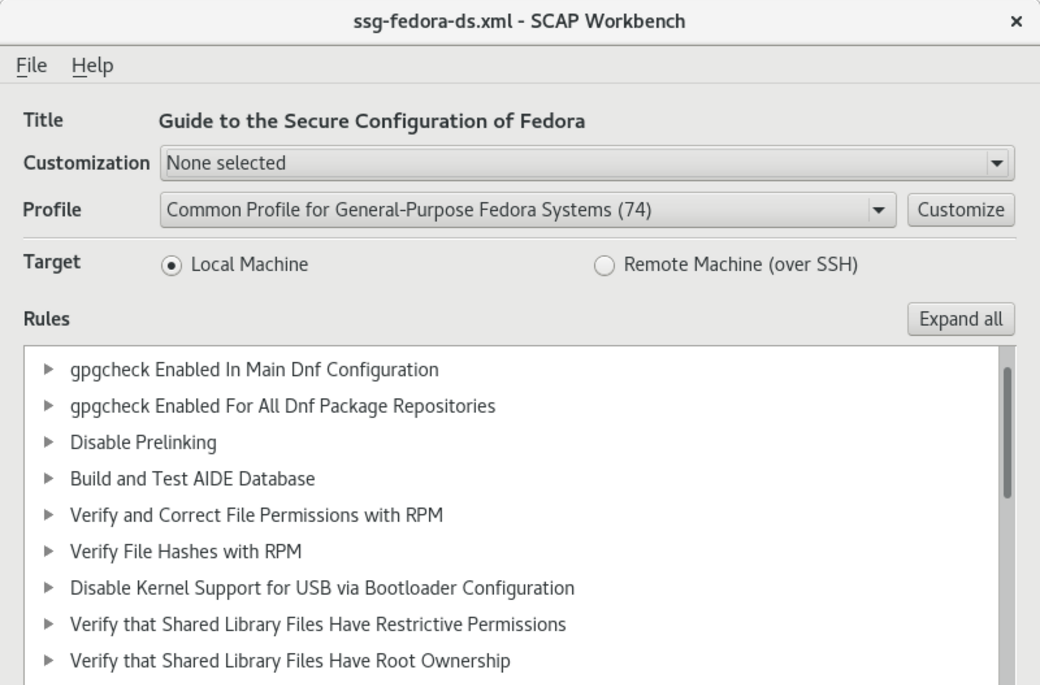
OpenSCAP provides a suite of automated audit tools to examine the configuration and known vulnerabilities in your software, following the NIST-certified Security Content Automation Protocol (SCAP).
You can create your own custom assertions and rules and routinely check that any software deployed in your organization strictly abides.
This set of tools is not only focused on security itself, but also on providing the formal tests and reports that you may need to meet an official security standard.
Docker context: The OpenSCAP suite provides a Docker-specific tool oscap-docker to audit your images, assessing both running containers and cold images.
16. REMnux
Homepage: https://remnux.org/
License: Open Source.
Use Cases: Forensics.
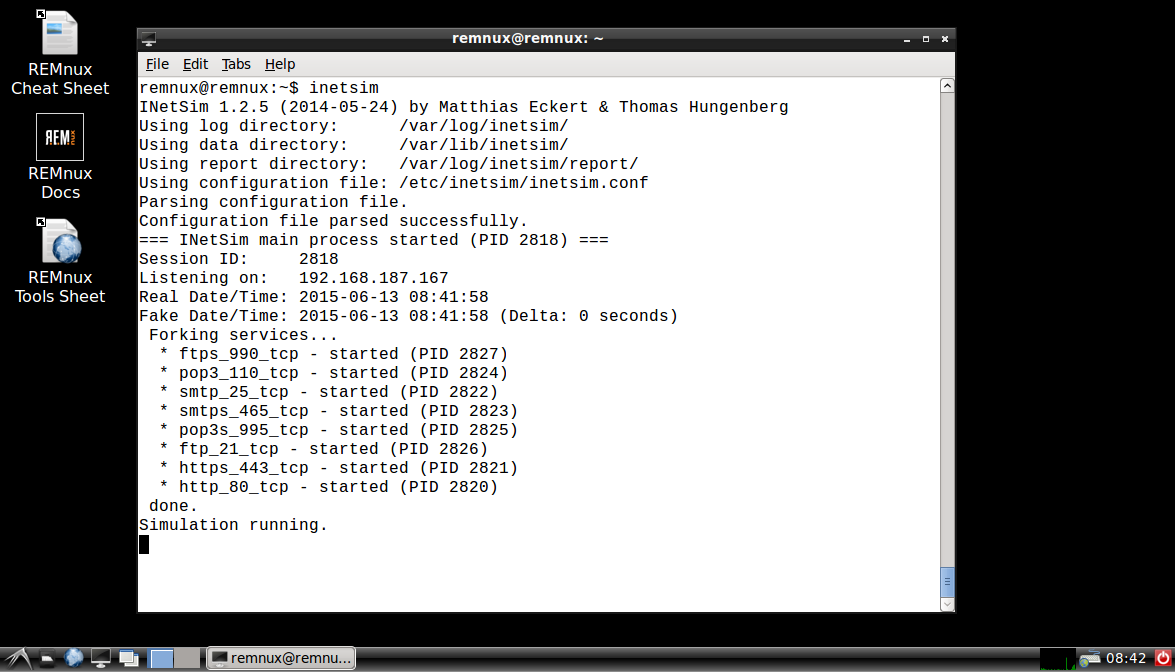
A security-oriented distribution based on Ubuntu. REMnux is a free Linux toolkit for assisting malware analysts with reverse-engineering malicious software, commonly known as forensics. As you can guess, this system bundles a vast amount of pre-installed analysis and security tools: Wireshark, ClamAV, tcpextract, Rhino debugger, Sysdig, vivisect... just to name a few.
REMnux aims to be the swiss knife that you carry around in a USB stick in case you suspect any of your systems have been compromised.
Docker context: The REMnux project conveniently provides several of its integrated security tools as Docker containers, so you can instantly launch difficult-to-install security applications when you most need them.
17. SELinux
Homepage: https://selinuxproject.org
License: Open Source.
Use Cases: Runtime protection, Mandatory Access Control (MAC).
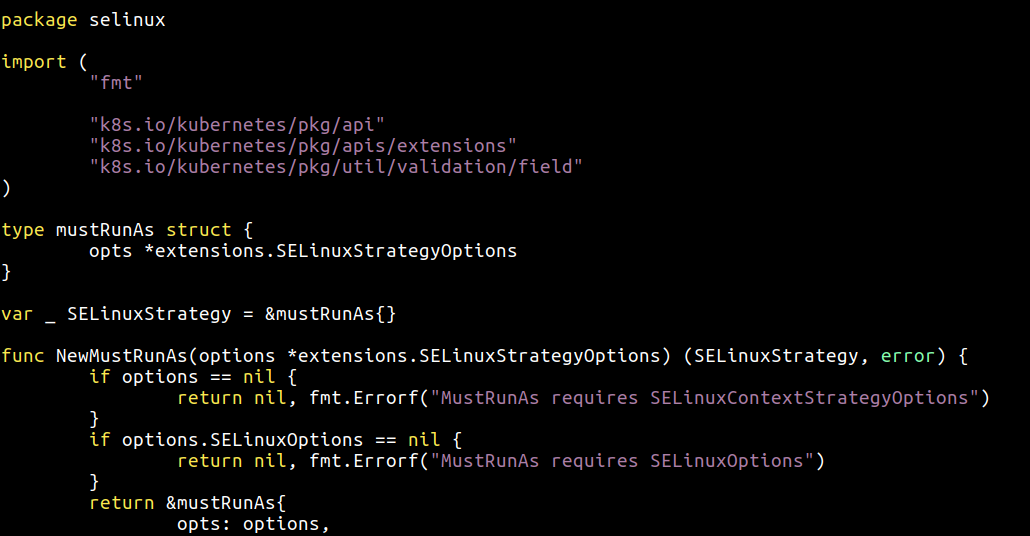
Security-Enhanced Linux (SELinux) is a Linux kernel security module. It is often compared with AppArmor, and it's also a Mandatory Access Control system. SELinux provides security capabilities from mandatory access controls to mandatory integrity controls, role-based access control (RBAC) and type enforcement architecture.
SELinux has a reputation for being particularly complex but powerful, fine-grained and flexible.
Docker context: Similarly to AppArmor, SELinux offers an extra layer of access policies and isolation between the host and the containerized apps.
18. Seccomp
Homepage: https://www.kernel.org
License: Open Source.
Use Cases: Runtime protection, Mandatory Access Control (MAC).
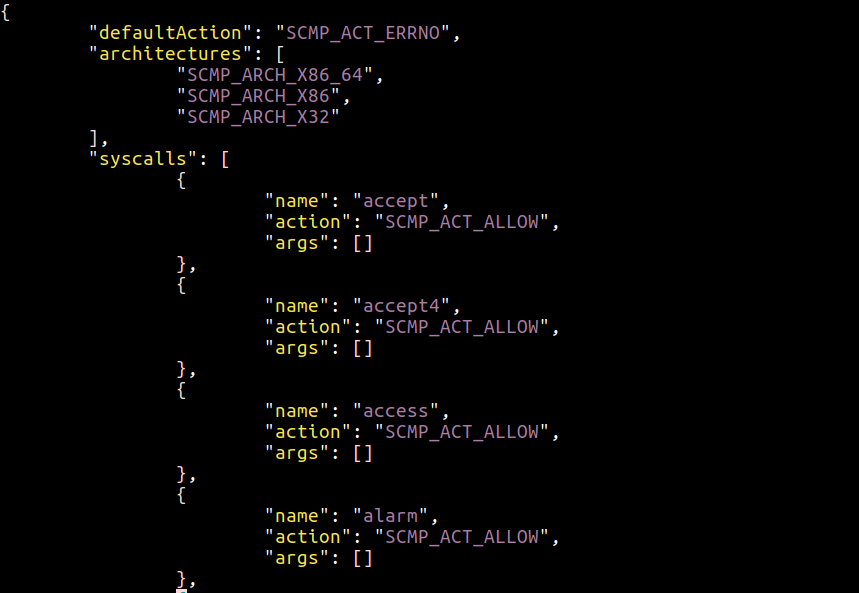
Seccomp is not so much a tool but rather a sandboxing facility in the Linux kernel. You can think of it as an iptables rules-based firewall but for system calls. Newer versions use Berkeley Packet Filter (BPF) rules to filter syscalls and control how they are handled.
With Seccomp, you can selectively choose which syscalls are forbidden/allowed to each container. For example, you can forbid file-permissions manipulations inside your container.
You may have noticed the similarities with Falco. Both are closely related to the Linux Syscall API. Unlike the others, Falco integrates a rich, high-level, container-specific context to build rules.
Docker context: Docker has used Seccomp since version 1.10 of the Docker Engine, Docker has its own JSON-based DSL that allows you to define profiles that will be compiled to seccomp filters.
19. StackRox
Homepage: https://www.stackrox.com
License: Commercial.
Use Cases: Runtime protection, machine learning, pre-production analysis.
StackRox feature proposal revolves around the concepts of "Adaptive security" and auto-discovery of components and behaviors. Highly focused on machine learning, StackRox aims to provide security that will evolve with your platform.
StackRox provides the usual features of commercial security platforms like cold image scanning or default security profiles a la SELinux.
StackRox understands containers and the images in your environment but can't enforce policies-based services determined by your orchestrator. They focus more on pre-production and run-time workloads rather than forensics and incident response.
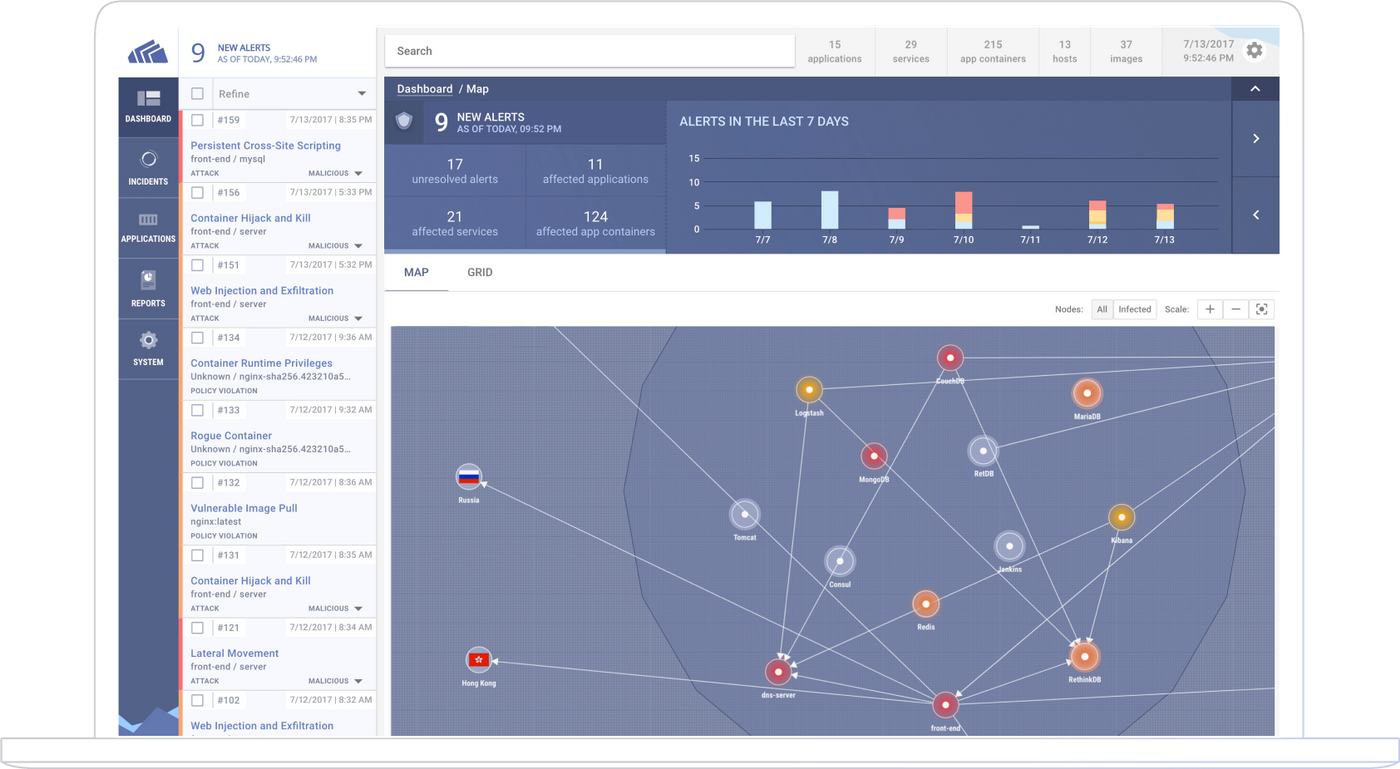
20. Sysdig Secure
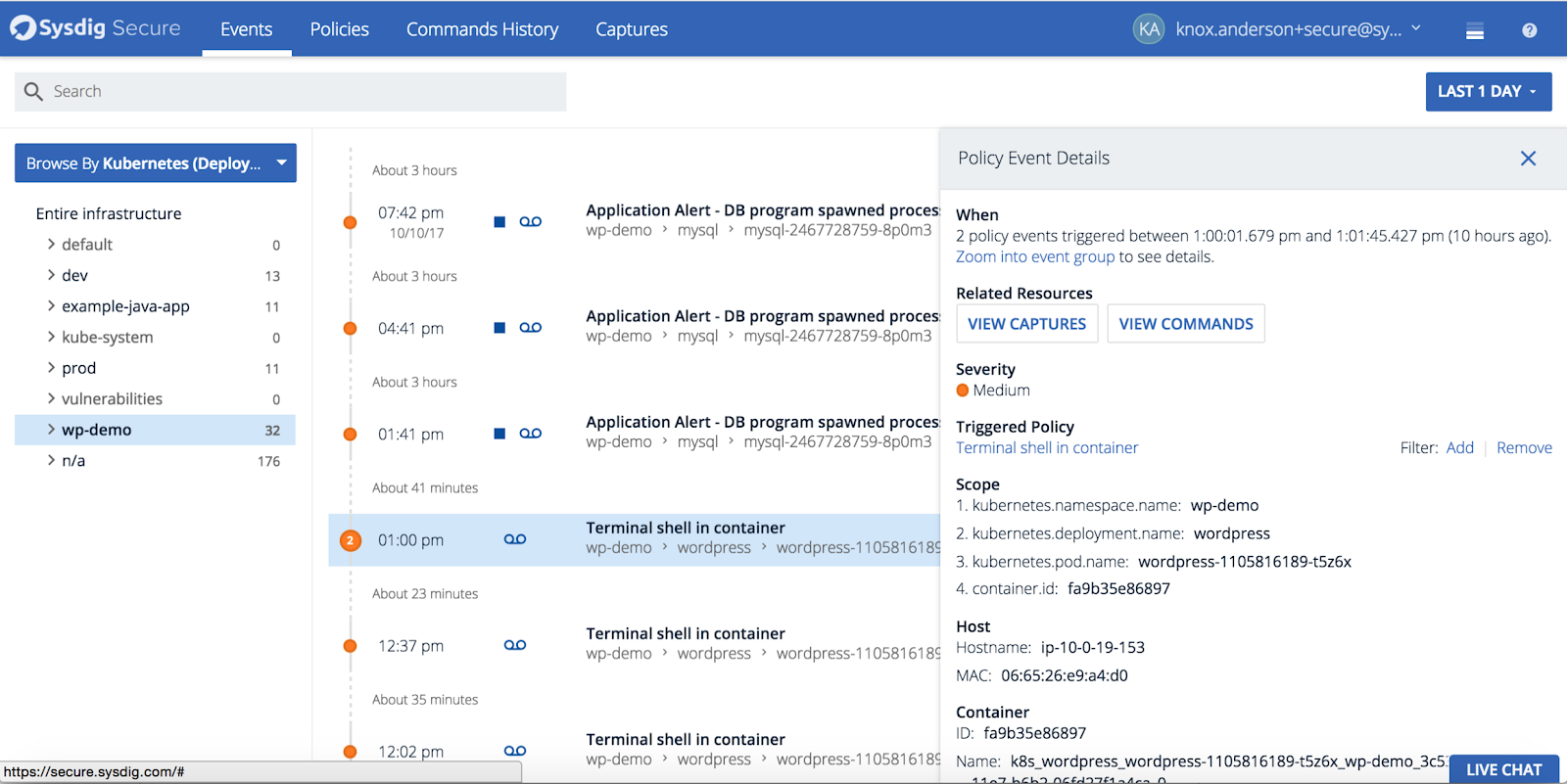
Homepage: https://www.sysdig.com/product/secure
License: Commercial
Use Cases: Runtime security, forensics and audit, hybrid environments (containers and traditional deployment), performance monitoring and troubleshooting, available both as SaaS and on-prem.
Sysdig Secure is a powerful run-time security and forensics solution for your containers and microservices. Secure is part of the Sysdig Container Intelligence Platform, and as the rest of the family comes out of the box with deep container visibility and container orchestrator tools integration, including Kubernetes, Docker, AWS ECS, and Mesos.
Sysdig Secure protects your entire infrastructure: containers and hosts as well as the logical services that run on top of them. Sysdig Secure also provides full-stack forensics capabilities for pre- and post-attack investigation.
Sysdig provides full performance monitoring and troubleshooting for your environment. A single instrumentation both for monitoring and security with no added overhead.
21. Sysdig
Homepage: https://www.sysdig.org/
License: Open source, commercial products built on top of the free technology.
Use Cases: Anomalous behavior debugging, forensics.
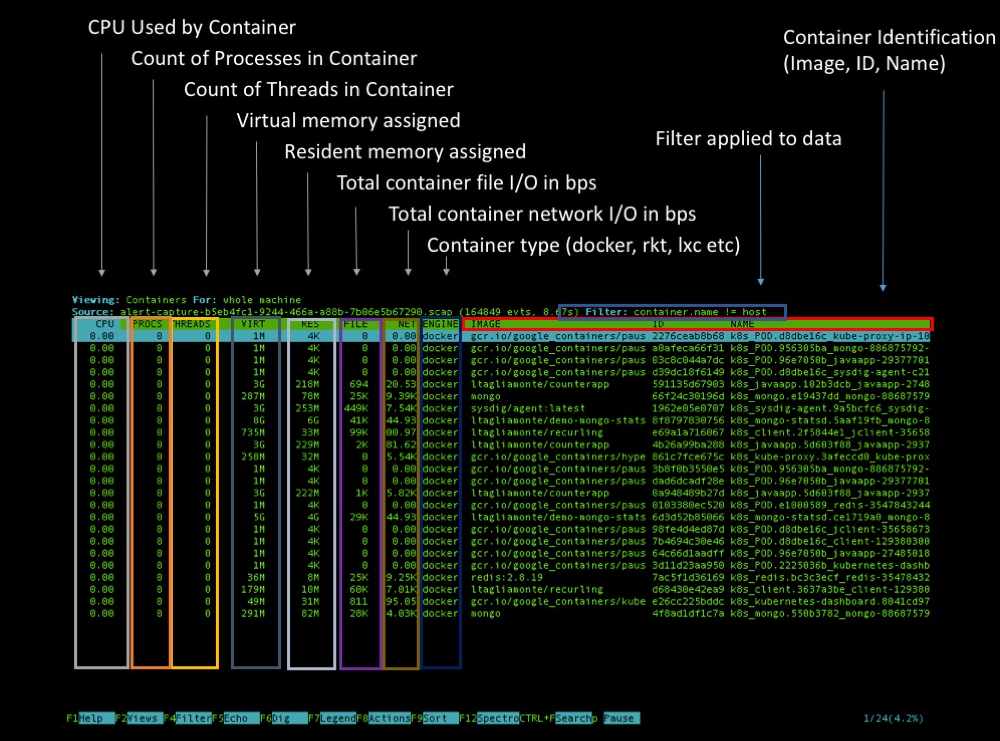
Sysdig is a full-system exploration, troubleshooting, and debugging tool for Linux systems. It records all system calls made by any process, allowing system administrators to debug the operating system or any processes running on it.
Sysdig has a command-line interface with a syntax similar to tcpdump and a ncurses interface to visually navigate and filter through the events, in a similar fashion to htop or Wireshark. The system call capture files allow you to perform forensics on your containers even if they are long gone.
22. Tenable Flawcheck
Homepage: https://www.tenable.com/flawcheck
License: Commercial.
Use Cases: Pre-production analysis, vulnerability newsfeed.
Tenable, the company perhaps best known for Nessus, the security scanner, acquired Flawcheck, a specific container-focused security solution.
FlawCheck, like other commercial tools in this list, stores container images and scans them as they're built, before they can reach production. FlawCheck leverages Tenable/Nessus know-how and database of vulnerabilities, malware and intrusion vectors, and adapts it to containerized and agile CI/CD environments.
23. Twistlock
Homepage: https://www.twistlock.com/
License: Commercial.
Use Cases: Pre-production analysis, runtime protection, compliance & audit, etc.
A commercial security suite built to support containerized environments: vulnerability management, access control, and image scanning-based standards compliance.
Twistlock integrates with your continuous integration/continuous delivery pipeline, providing native plugins for popular tools like Jenkins or TeamCity and callable webhooks, so you can trigger the indexing and scanning process for every build and testing environment. Twistlock is known for its popular scanning technology but its run-time security only enforces actions against containers, not their underlying hosts, or orchestrated services.
Published at DZone with permission of Mateo Burillo, DZone MVB. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments