10 Security Best Practices for SaaS
SaaS security encompasses a range of measures and protocols designed to protect sensitive data and ensure the safety of users within a SaaS environment.
Join the DZone community and get the full member experience.
Join For FreeIn this article, we’ll discuss the importance of guarding your SaaS and the SaaS Security best practices you must implement in your Security checklist to ensure the proper functioning of your app. The seemingly unstoppable growth of SaaS platforms in the industry has made the discussion of securing SaaS Applications a need among organizations.
We will also be talking through the challenges and risks the area faces, as well as the regulatory standards that should frame all SaaS application development.
What Is SaaS Security?
SaaS (Software as a Service) security refers to the measures and practices implemented to protect data and applications delivered over the internet via SaaS platforms.
SaaS security encompasses a range of measures and protocols designed to protect sensitive data and ensure the safety of users within a SaaS environment. It involves robust encryption, authentication mechanisms, access controls, and regular audits to prevent unauthorized access, data breaches, and potential vulnerabilities.
Why Is SaaS Security Important?
Before diving deeper into the world of SaaS application security, let’s elaborate on its importance. As companies adopt the SaaS model into their business, there’s an amplification of data privacy concerns.
We need to remember that talking about a company’s adoption of SaaS models implies the recollection of corporate data that can be found in the form of financial data, HR records, customer data, and other critical business information. That is why it is essential for companies to keep all this information safe, as it ending up in the wrong hands could potentially threaten the organizations’ stability and well-being.
That’s why SaaS security is crucial for several reasons:
- Protecting sensitive data: It ensures that sensitive information remains secure and out of the hands of hackers, malicious insiders, and other cyber threats.
- Preventing severe consequences: Strong security measures help avoid serious repercussions such as legal liabilities, reputational damage, and customer loss.
- Building customer trust: Effective SaaS security increases customer confidence in the provider’s ability to safeguard their data.
- Compliance: It ensures adherence to security standards and regulations.
- Application and data protection: It protects applications and data from cyber threats, significantly reducing the risk of data breaches and other security incidents.
Challenges and Risks for Security in SaaS
Some of the leading security challenges and risks all SaaS companies must look out for revolve around data breaches, account hijacking, misconfigurations, and access management. Prior to learning about the SaaS security practices you can implement, let’s familiarize ourselves with these menaces.
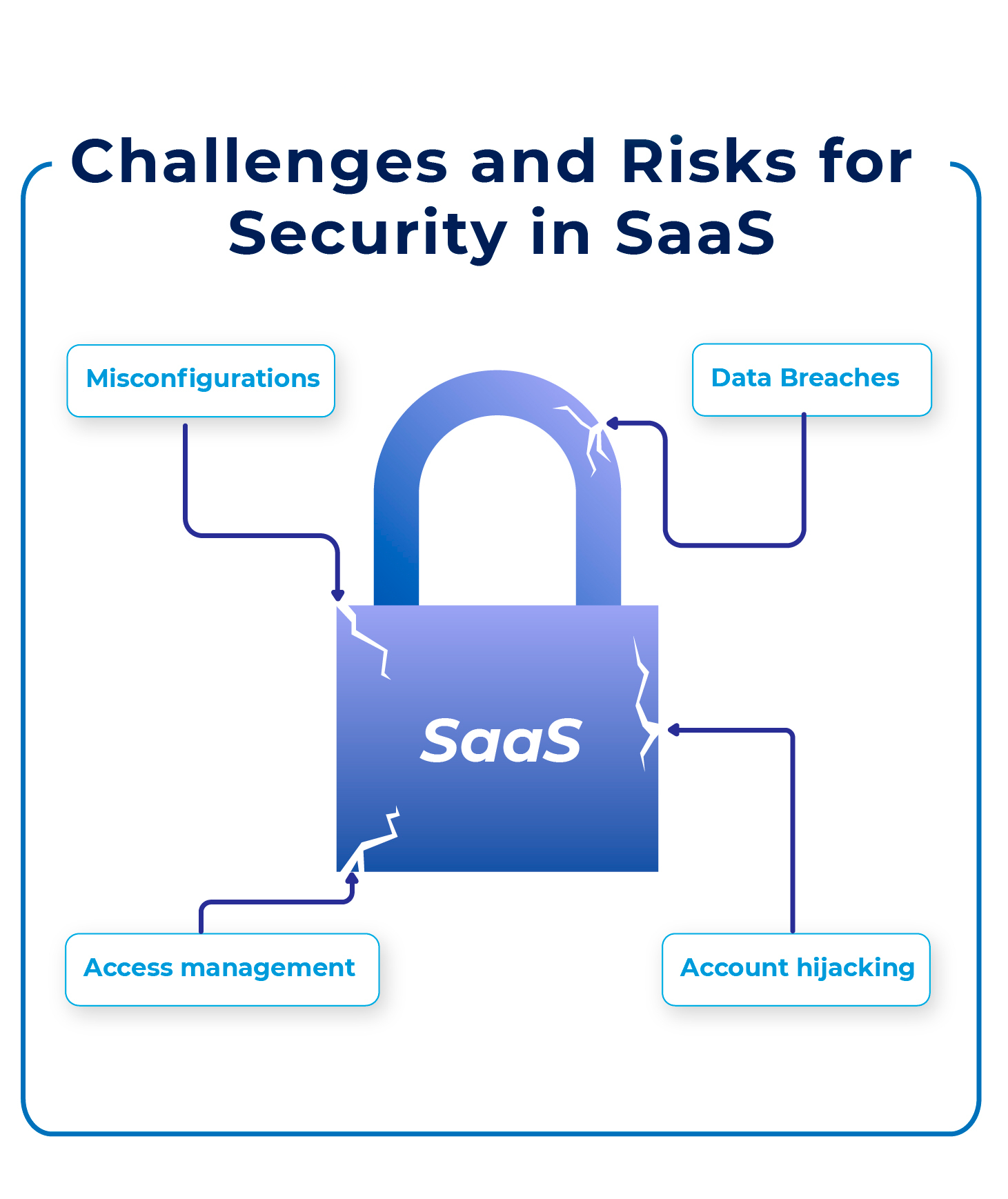
Data Breaches
This type of incident is a daily threat to organizations. The viewing, access, or usage of sensitive data by an unauthorized individual is considered a security violation and can lead the company to severe problems. Therefore, an application provider must have strong measures to prevent a security breach from happening.
Account Hijacking
This common form of cyber-breach is also known as a “ransomware attack.” When a cybercriminal has access to its target network, intellectual property can be damaged or even lost. Criminals also use these attacks to extort companies and gain a monetary price.
Misconfigurations
The layers of complexity in a SaaS system can increase the chances of misconfigurations arising. When there’s a problem with a component or the configuration is incorrect, it becomes vulnerable to cyberattacks. This situation also affects cloud infrastructure availability. It’s particularly pertinent in containerized environments, where a combination of the possibility for misconfigurations and issues with monitoring create container security conundrums.
Access Management
As we mentioned before, sensitive data makes access management critical for every SaaS Application. Customers need to be aware of whether an access point into the public cloud is capable of exposing their confidential information. Network security issues, poor patching, and lack of monitoring are avoidable situations when designing suitable access control systems.
SaaS Security Best Practices for Your Application
From a security checklist to security-focused SDLC, here are some of the best SaaS security practices you must adopt when providing the best SaaS Application Security.
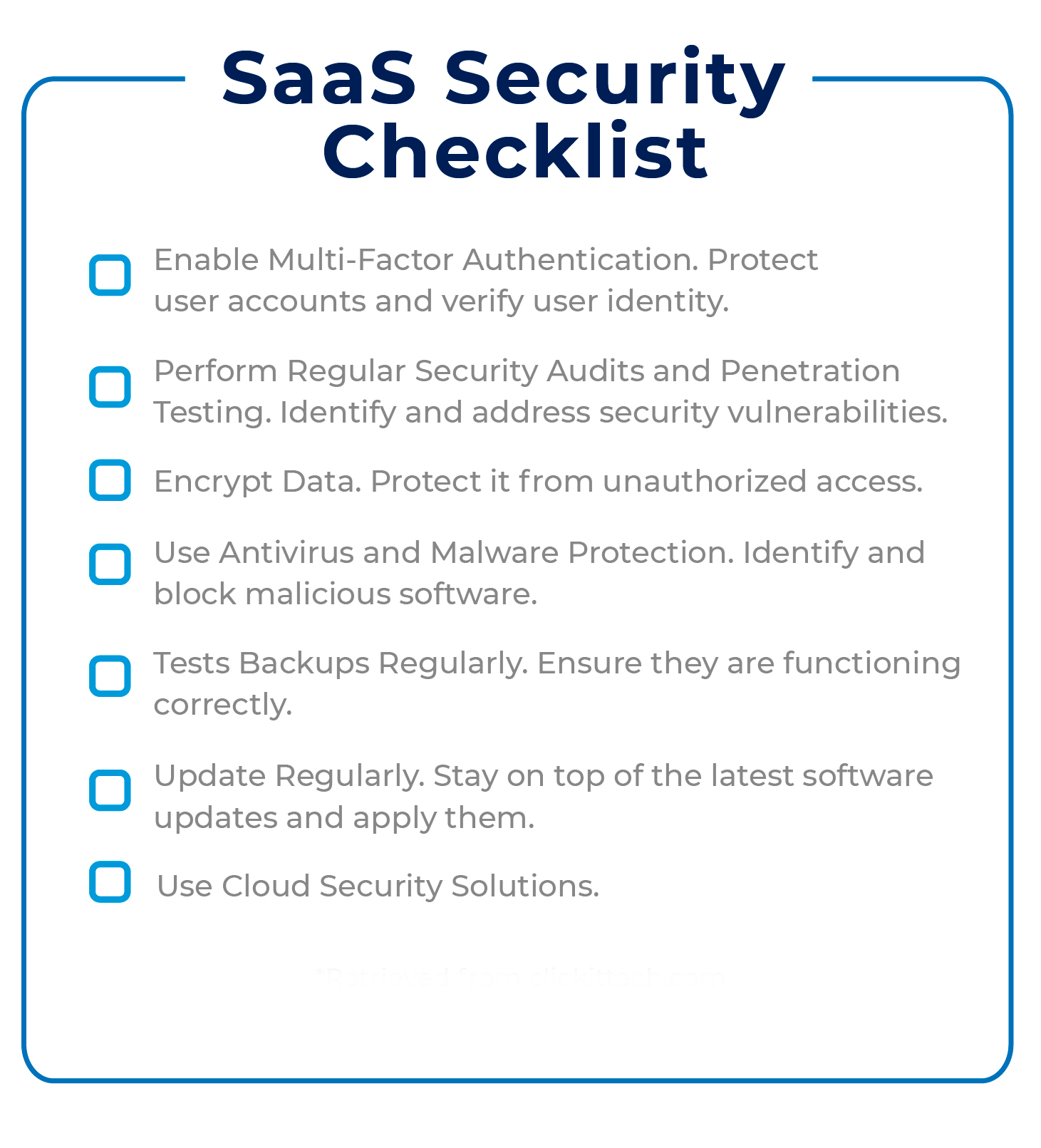
1. SaaS Security Checklist
Your company must make an effort to implement a strong security culture that establishes the organization’s security requirements with a SaaS security checklist. Depending on the app’s nature, the checklist elements may vary. Nevertheless, it should be reviewed and updated constantly, as priorities can change and different threats arise.
A security checklist can also help you when choosing a cloud service provider. Clarifying your needs facilitates selecting a supplier that fulfills your expectations.
Here’s an example of what a SaaS Security Checklist could look like:
- Enable multi-factor authentication. Protect user accounts and verify user identity.
- Perform regular security audits and penetration testing. Identify and address security vulnerabilities.
- Encrypt data. Protect it from unauthorized access.
- Use antivirus and malware protection. Identify and block malicious software.
- Tests backups regularly. Ensure they are functioning correctly.
- Update regularly. Stay on top of the latest software updates and apply them.
- Use cloud security solutions.
2. Map Your Data
To provide top-level protection, mapping, classifying, and monitoring all data is critical. Even if the information is in transit, use, or at rest, SaaS developers need to see it and follow the necessary measures to secure its preservation. Having a detailed understanding of your data helps identify potential threats and vulnerabilities.
Here are some steps you can follow when mapping your data:
- Establish security frameworks. They should outline the policies and controls you use to address security in your application.
- Identify security goals. What security goal do you want to achieve? How are you going to measure them?
- Identify assets. What assets do you need to protect? Make sure to include data, services, and systems.
- Risk assessment. By developing a risk assessment, you will identify vulnerabilities and potential threats. This can also help to prioritize the threats based on likelihood and severity.
- Security controls. Implementing security controls protects your data and addresses identified risks.
- Monitor security. Monitor regularly and modify when needed.
- Educate users. Users should be aware of the importance of data security and the implemented controls.
- Respond to incidents. Develop a response plan for when an incident happens. Practice it regularly to be prepared.
3. Identity Access Management Controls (IAM)
Identity and access management solutions ensure that users access only the resources they require. Specific processes and user access policies determine this entrance. Programs need to be aware of who accessed what and when.
Preventing unauthorized access helps avoid data leaks, protects users from hacking, and ensures compliance with privacy regulations.
- When implementing IAM controls, you can start by establishing user authentication protocols. That way, you ensure the authentication of all users before granting them access to the application. You can use two-factor authentication, biometrics, or other secure methods.
- Create user profiles and set up user access controls tailored to users’ needs. Users will only be granted access to areas needed for their jobs.
- Implement role-based access control by assigning roles to users and limiting their access to resources based on those roles.
- If you want to detect suspicious or unauthorized behavior, it’s a good idea to monitor users’.
- You can also create audit trails and track user activity. You’ll be able to identify and address any unauthorized activity.
- Create secure passwords and enforce password expiration so that users change them regularly.
- Update security settings regularly.
4. Data Encryption
Although many vendors provide some form of encryption, extra careful clients tend to apply their own (added) encryption. This way, data at rest (in storage) and in transit can be protected through a local hardware facility, using Transport Data Encryption (TDE), implementing a Cloud Access Security Broker (CASB), or with methods like Transport Layer Security (TLS).
SaaS applications tend to use TLS to protect data in transit. TLS is a security protocol that encrypts data sent over the Internet. In it, the server (e.g., SaaS security provider) and client establish a secure, encrypted connection using public key cryptography. The client and server exchange cryptographic keys and then use them to create a secure connection.
Different data encryption algorithms can be helpful in keeping your SaaS Application Security at the best level. Let’s review some of the most popular ones.
Advanced Encryption Standard
AES is currently the trusted US Government encryption Standard. It is also standard by numerous organizations, as it’s primarily considered impervious to all attacks.
AES belongs to the symmetric algorithm category and uses a symmetric book cipher that comprises up to three key sizes: 128, 192, or 256 bits. Each key size has its rounds of encryption: 128 bit = ten rounds, 192 bit = 12 rounds, and 256 bit = 14 rounds. A round takes place every time plaintext is turned into cipher text.
It’s believed that one attack against the AES algorithm would require around 38 trillion terabytes. Nowadays, such computing power and data storage are simply unfeasible.
RSA
The Rivest-Shamir-Adleman algorithm is a central feature in many protocols, such as SSH, OpenPGP, SSL/TLS, and S/MIME. This public-key encryption algorithm belongs in the asymmetric category due to its two keys involved in encryption and decryption.
RSA’s popularity remains due to its key length, which typically varies between 1024 and 2048 bits long. As the key length increases, it becomes harder to break the algorithm.
Blowfish
The go-to encryption method for businesses and industries, as it’s one of the most flexible methods available and free in the public domain. The Blowfish algorithm takes a plaintext message and a key as input. Using the key, it generates subkeys that encrypt the plaintext. Then, the algorithm splits messages into 64-bit blocks of data and encrypts them individually. The process continues, and the algorithm repeats the process 16 times.
Despite its seemingly long process, many know and prefer Blowfish for its speed and overall effectiveness.
Twofish
It is one of the fastest encryption algorithms and an excellent choice for hardware and software environments. Twofish is a symmetric-key block cipher that divides a plaintext message into blocks of 128 bits. Then, it uses a key of either 128, 192, or 256 bits to encrypt each block. There are several rounds of substitution, XOR operations, and permutation in the encryption process.
Twofish, like Blowfish, is also accessible to anyone interested in using it.
5. Data Deletion Policy
A strong commitment some companies opt to make when ensuring their customer’s security is enforcing a strict data deletion policy. Systematically deleting customers’ information is often a legal requirement for organizations and, consequently, a priority. However, they must execute the process so that it doesn’t affect the generation of relevant information logs that need to be maintained.
Data deletion policies ensure the customers’ control over their data. Providers of security in SaaS can also make sure to stay compliant with applicable laws and regulations while upholding the trust their customers have in them.
Aspects a data deletion policy should consider include the following:
- Data deletion timeline: The organization must delete customers’ data within the schedule.
- Deletion methodology: The company must follow a specific methodology when deleting the data.
- Customer access rights: Customers must have an easy way to access their data at any time.
- Data backup policies: The organization must follow specific rules if it needs to keep data stored.
6. Data Loss Prevention (DLP)
DLP is useful when working with sensitive data as it monitors outgoing transmissions and can even block them if necessary. It prevents personal devices from downloading sensitive data, blocking malware or probable hackers in their ill-intentioned attempts. DLP is especially helpful when dealing with IP protection, data visibility, and personal information compliance.
If your organization has substantial intellectual property to protect, you can use context-based classification, a DLP solution that classifies the IP in structured and unstructured forms. This can save the organization against unwanted data exfiltration.
Gaining additional visibility into your data movement is easy when using a comprehensive enterprise DLP solution. It can help you track your data and see how individual users in your organization interact with it.
DLP can also identify and classify personal information or sensitive data. It monitors activities surrounding that data and provides details needed for compliance audits.
7. Audits and Certifications
When keeping data with the highest level of security, there are helpful regulatory compliances and certifications such as the PCI DSS (Payment Card Industry Data Security) and the SOC Type II.
SaaS providers regularly undergo audits to ensure data is fully protected when stored, processed, and transmitted.
Regulatory Standards for Security in SaaS
Having multiple data centers, continuous periodic penetration testing, data audits, and ensuring integration are some general requirements regarding SaaS Application Security.
It is also essential to maintain compliance with regulatory standards such as:
- PCI DSS: Security standards that maintain a secure environment in all companies that process, store, or transmit credit card information.
- HIPAA: The Health Insurance Portability and Accountability Act protects sensitive patient health data from being disclosed without consent.
- SOC 2: The Systems and Organization Controls 2 provide auditors with helpful guidance when evaluating security protocols.
8. Cloud Access Security Brokers (CASBs)
CASBs can be of great help for your SaaS Application Security. They assist in identifying when members of organizations use unauthorized SaaS products. They act as control points capable of setting policy, monitoring behavior, and managing risks across a SaaS stack.
With CASBs, IT departments gain more significant data usage and user behavior visibility. They can also eliminate security misconfigurations and correct high-risk user activities. Some of their security services and capabilities include providing compliance reporting, enforcing data security policies (such as encryption), security configuration audits, and more.
CASBs secure data that flows to and from in-house IT architectures and cloud vendor environments. They also protect data through encryption, making it unreadable to outside parties. Through malware prevention, CASBs shelter enterprise systems against cyberattacks.
Moreover, CASBs provide capabilities not ordinarily obtainable in traditional controls like enterprise firewalls and secure web gateways (SWGs). They deliver policy and governance concurrently across various cloud services while providing granular visibility and control over user activities.
9. Risk Level
Just as with the security checklists, assessing the risk level of a SaaS vendor can define an organization’s security controls. The knowledge of what they are against to will affect the control over data access, processing, and monitoring. Consider the following tips when assessing your SaaS vendor:
- Check security policies: Review your vendor’s security policies and ensure they have the safety protocols to protect your data.
- Read reviews: Other customers’ experiences may give you a better idea of the vendor’s reliability.
- Verify compliance with regulations: Your vendor must be compliant with the necessary standards and regulations.
- Consult industry experts: They can give you an objective third-party opinion of the vendor and its risk levels.
10. Software Development Life Cycle (SDLC) Focused on Security
Organizations secure every phase of their SaaS enterprise by incorporating a security focus into the software development process. Your application will become more robust, and the security profile of the SDLC will go even further.
Developer teams tend to defer security-related activities until the testing phase. Nevertheless, these checks can be superficial, as most of the critical design and implementation have already been completed. When the team discovers problems this late in the SDLC process, it can often cause delays and increase the overall price of the production.
A security-focused SDLC can identify potential threats early on, meaning you can address them even before they become a problem.
You can also prevent data breaches and ensure customer trust and satisfaction.
Focusing your SDLC on security means implementing security steps in each cycle phase.
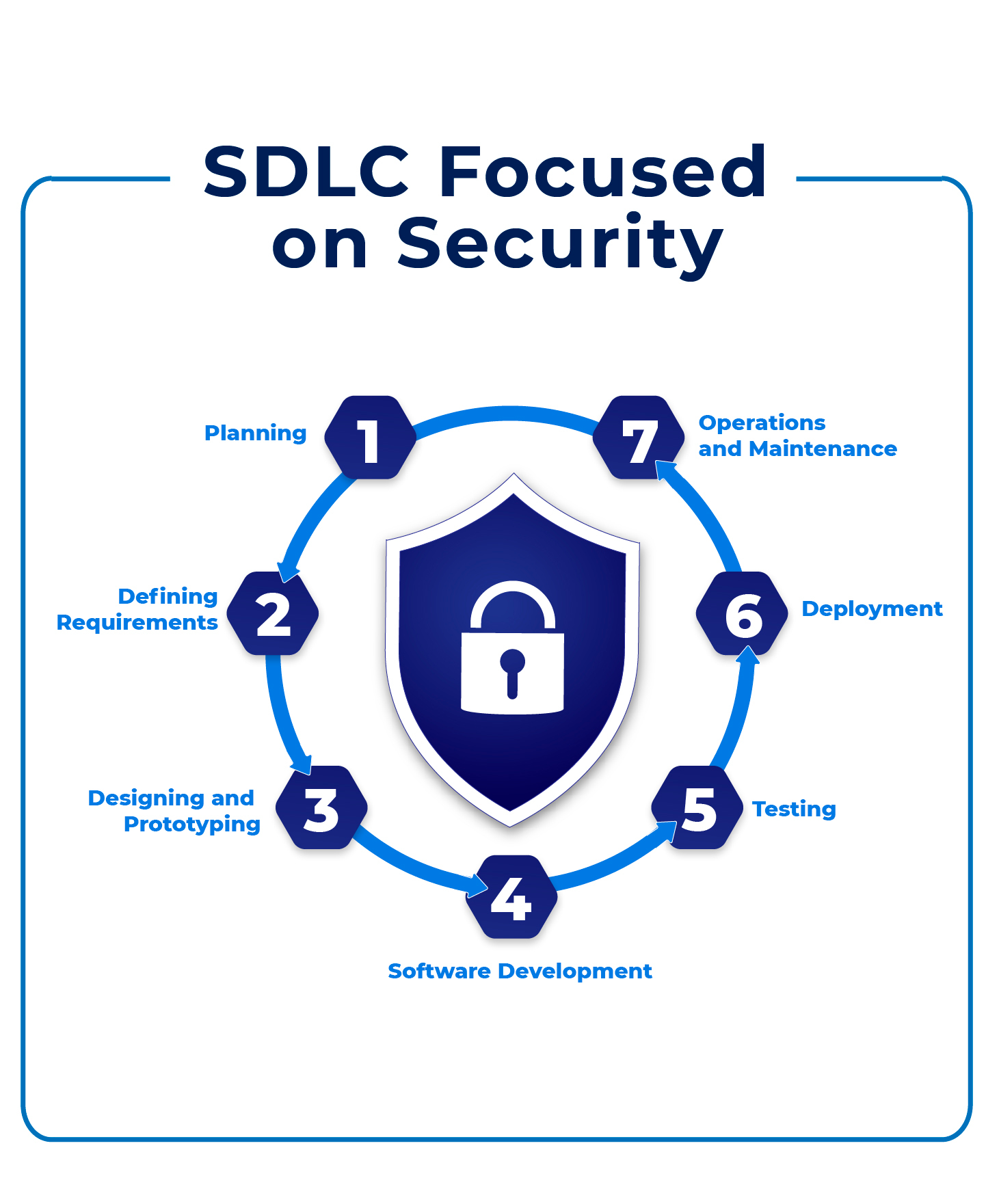
- Planning: Identify the possible risks and security threats. Evaluate the potential impact of security incidents on the enterprise.
- Defining requirements: Understand and incorporate security, compliance, and regulatory requirements as part of the defining functional requirements.
- Designing and prototyping: Security considerations should be an integral part of the architecture plan. Engaging in threat modeling is also essential.
- Software development: Educate developers on incorporating security testing tools (e.g., OWASP Zed Attack Proxy, SQLMap, Nmap, etc.) and the importance of secure coding practices.
- Testing: Perform security testing like interactive application security testing and static analysis. Implementing code review processes is also a good idea.
- Deployment: Continuously review the configurations for security.
- Operations and maintenance: Monitor regularly to detect threats and prepare to respond in case vulnerabilities or intrusions occur.
Conclusion of SaaS Security
Arming your SaaS application and SaaS Security checklist with the best practices is, now more than ever, a fundamental aspect of SaaS development teams. That is to say, the consequences of taking it lightly or ignoring its importance can affect the organization’s functioning and users’ security.
Published at DZone with permission of Alfonso Valdes. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments